-
Notifications
You must be signed in to change notification settings - Fork 2k
chore: secure workflows permission #7024
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Conversation
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
| @@ -9,6 +9,8 @@ on: | |||
| jobs: | |||
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Please add top-level permissions:.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
permissions: in top-level will cover permission all jobs, And i think no need set permission per job when top-level already write exclude job check-version must set permission: read. Agree?
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I think generally we should set top-level permissions: read only.
Top level permissions: is the default, and it can be overridden in jobs.
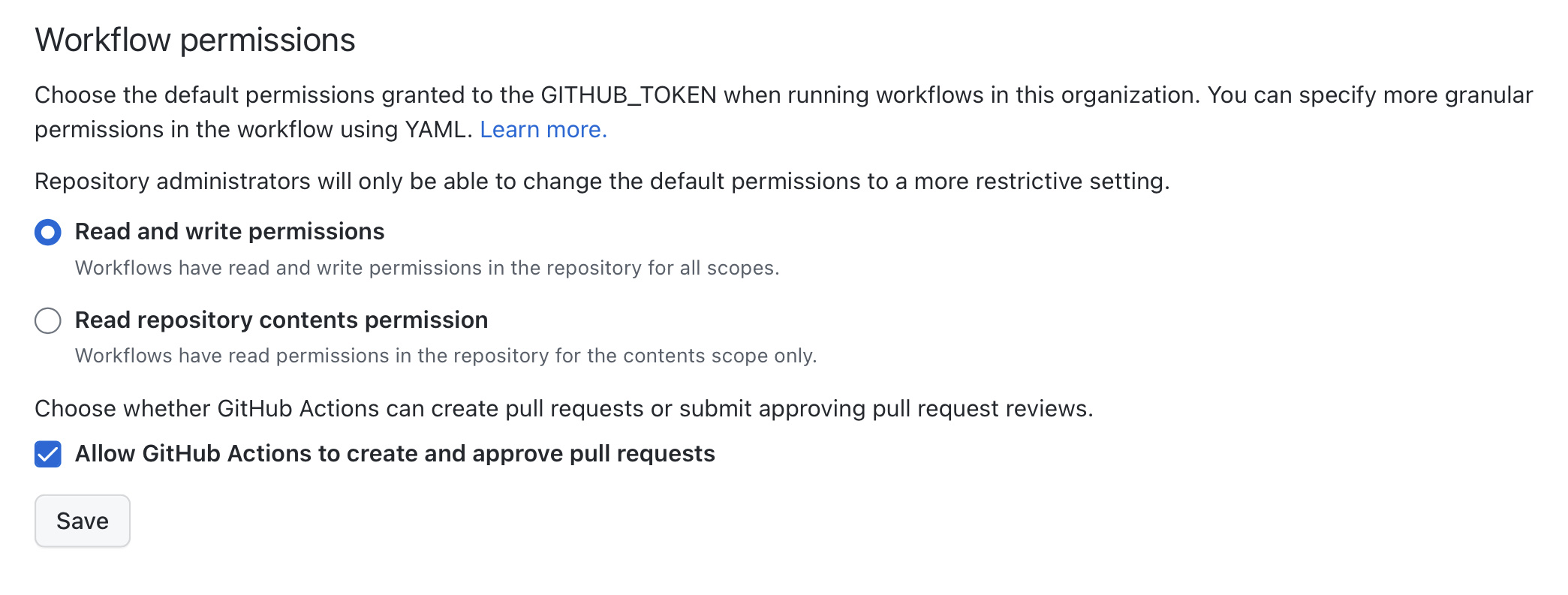
I don't know the default setting of this organization. So if it is read write permissions, jobs without permission can write. It is not safe to supply chain attacks.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
You can set default permission in organization, open https://github.com/organizations/codeigniter4/settings/actions and find Workflow permissions in bottom
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I have no permission to access the URL.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Yes.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
or only owner this organization can access this setting
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Default org permission should be read-only. Adding write permissions should be done on a per-workflow or per-job basis only.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Yes, said @paulbalandan, and we must not forget that one day if we want to change permissions at the organizational level, we must include permission read at the top-level.
Btw, i am @ddevsr. Waiting review recovery account.
|
SCSS error was fixed. Please rebase when you update. |
|
Thanks for spearheading this! I will have to read more in depth on the individual permissions and scopes. Please address @kenjis' questions in the meantime. |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Do we still need all the "contents: read" directives once the org change is made?
Yes. If we would change the org setting accidentally or by any reason, all GA flows will have write permissions. |
|
Organization repository workflow permissions have been set to "read". Please keep an eye on these workflow runs over the next few days. |
Description
Ref: twbs/bootstrap#36325 PHP-CS-Fixer/PHP-CS-Fixer#6644
Checklist: