fix(dashboard rbac): make a dashboard with no role assigned accessible only when PUBLISHED instead of DRAFT#22642
Conversation
…e only when it is PUBLISHED instead of DRAFT
There was a problem hiding this comment.
Congrats on making your first PR and thank you for contributing to Superset! 🎉 ❤️
We hope to see you in our Slack community too!
|
We have the same issue and I see this PR will solve the problem, I tested the modification in a docker in versione 2.0.1. |
|
Any news about the approval of this PR? |
Codecov Report
@@ Coverage Diff @@
## master #22642 +/- ##
==========================================
- Coverage 65.66% 55.79% -9.87%
==========================================
Files 1859 1859
Lines 71093 71096 +3
Branches 7777 7777
==========================================
- Hits 46680 39667 -7013
- Misses 22388 29404 +7016
Partials 2025 2025
Flags with carried forward coverage won't be shown. Click here to find out more.
📣 We’re building smart automated test selection to slash your CI/CD build times. Learn more |
|
@giovannipapini-agilelab is this PR ready for review? |
|
Hi @eschutho, yes, it is a quite basic fix but fundamental for |
|
I tried applying your changes, but still issue persists. I installed superset using pip |
|
It seems to work for us |
|
@giovannipapini-agilelab How will this behave if DASHBOARD_RBAC is enabled with no roles assigned in a published dashboard's properties? Will it gives access to every logged in user or will it fall back to dataset permissions ? |
It will fall back to user's dataset permissions. It seems to me the right behaviour, coherent with the text box under dashboard roles |
|
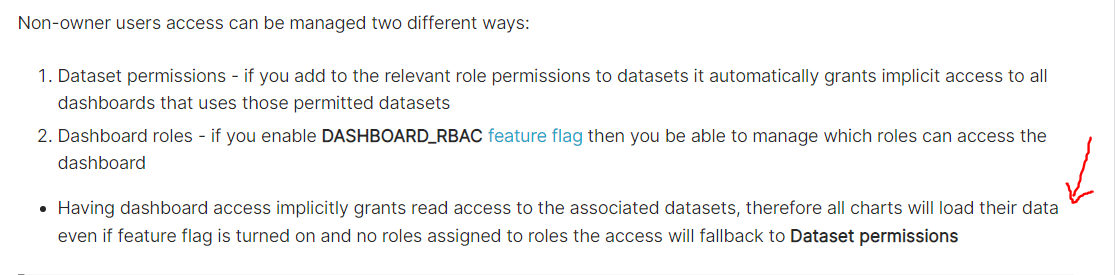
My understanding of this text:
is dashboard will be available to any logged in user which is then a security issue. |
|
We could also fix that text box writing something like
that is the most precise behaviour definition. |
|
IMO, correction of that text is also needed. Something like this as shown in this documentation https://superset.apache.org/docs/creating-charts-dashboards/creating-your-first-dashboard/#manage-access-to-dashboards
@amitmiran137 I feel there is a fullstop (.) missing in the documentation in here -> |
|
@mdeshmu may I add those also those fixes in this pr? |
|
@giovannipapini-agilelab I would love to see clarity in the texts. |
|
@giovannipapini-agilelab With your changes in this PR, Can you please test that if dashboard is published and no role is assigned to dashboard, is it accessible by a user with Public or Gamma Role ? |
Hi, we verified this case and in indeed the behaviour is this:
Imo this is the correct behaviour (and note that it is not the same as before this PR).
Probably we should fix the fallback behaviour, in this or in some other PR, what do you think @mdeshmu? |
|
Good summary @giovannipapini-agilelab. FYI I was testing out a separate feature on version 2.1.0rc1 and found that the DASHBOARD_RBAC behavior is slightly different from 2.01. If a dashboard is draft and has no RBAC role assigned, it still tries to load - its name appears in the browser - but it errors before it can load. I suppose this is the same behavior since it's trying to load, but heads up in case that complicates how this is discussed. |
|
Hi there, Just discovered this 'feature' whilst testing for our organisation: the fact that (currently) Draft dashboards provide a window for unauthorised users onto data they wouldn't normally be allowed to see, (if no RBAC roles are assigned) if this PR merges than those same unauthorised users will see the data when the dashboards are published. I'm surprised we don't simply delete the line of code in question, i.e. be explicit in the RBAC rules that if we want a world-readable dashboard we assign a role that we know all users have ? Why do we assume no roles == everyone cas access the data ? It is very likely users creating dashboards will forget to publish or unpublish their dashboards and not assign any RBAC rules, and will not understand the implications in terms of who can access their data between the two states. As an administrator this presents a risk, trusting the users to do the right thing here (manage the draft / published AND the RBAC rules) is not realistic for us. Can we make a plea for removing line 1994 completely, and require the user to add an explicit role instead ? -ivan |
|
@ivan-price-acted you may have missed this PR, which I believe addresses at least part of the permission issue: #23586 |
|
Hi @villebro indeed i had missed that and indeed that appears to address our concerns ! Looking forward to release 2.1.1 , thanks for the heads up ! |
|
I'm going to close this pr for #23586 with hopes that the latter covers this use case. |
SUMMARY
Minor bug fix on dashboard RBAC faulty behaviour
TESTING INSTRUCTIONS
See issue #22640
ADDITIONAL INFORMATION
'DASHBOARD_RBAC' = True